Zero Trust in Practice: How Systems Behave When Something Goes Wrong
Most security discussions focus on how to keep attackers out. Far fewer ask what happens after something goes wrong. Zero Trust is not about preventing every failure. It is about designing systems that remain stable when uncertainty appears.
Most discussions about security begin at the perimeter. The focus is on how to prevent attackers from getting in, how to harden the outer shell of a system, and how to reduce the likelihood of the first compromise. Firewalls, authentication mechanisms, encrypted connections, and access controls dominate the conversation. All of this is necessary, but it quietly avoids a more uncomfortable question: what happens when something fails anyway?
Experience shows that failure is not an anomaly. Credentials leak, configurations drift, dependencies change, and systems evolve faster than their original assumptions. In real environments, it is not a matter of if something goes wrong, but when. The decisive factor is not the initial mistake itself, but how the system reacts once that mistake has occurred.
This is where the difference between traditional architectures and Zero Trust thinking becomes visible. Not as a slogan, and not as a single product, but as a fundamentally different way a system behaves under uncertainty.
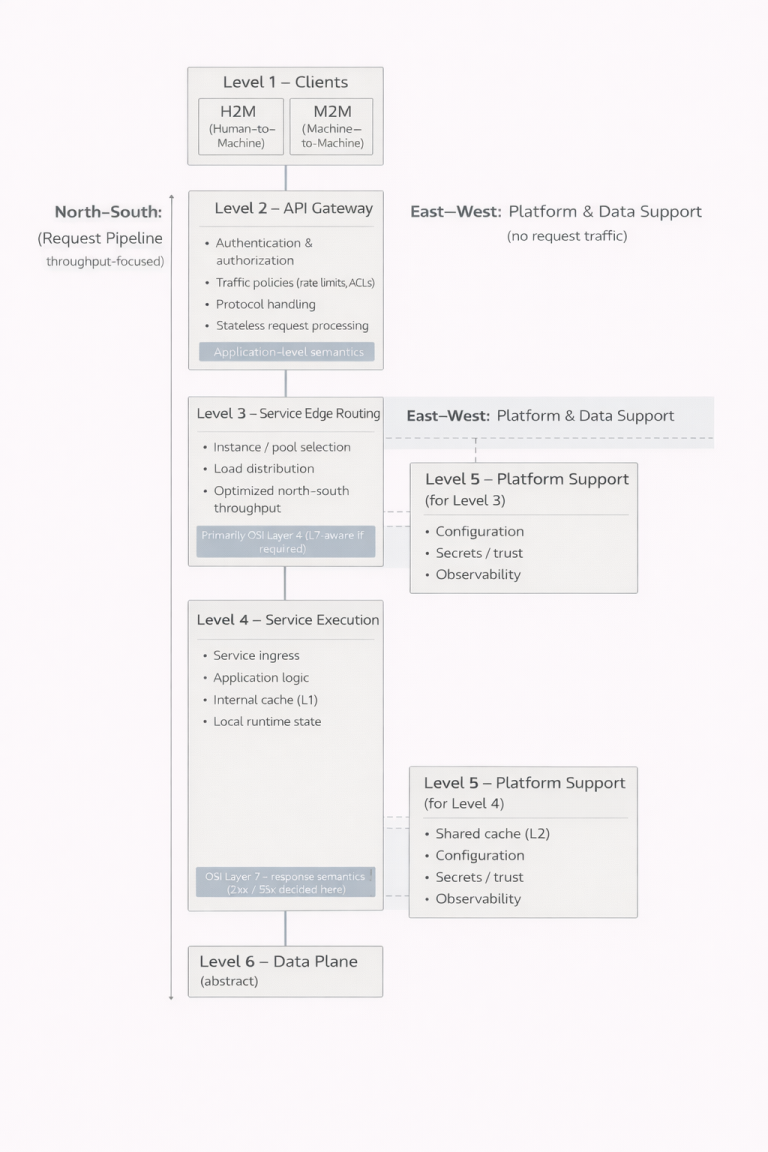
Two Ways of Thinking About Trust
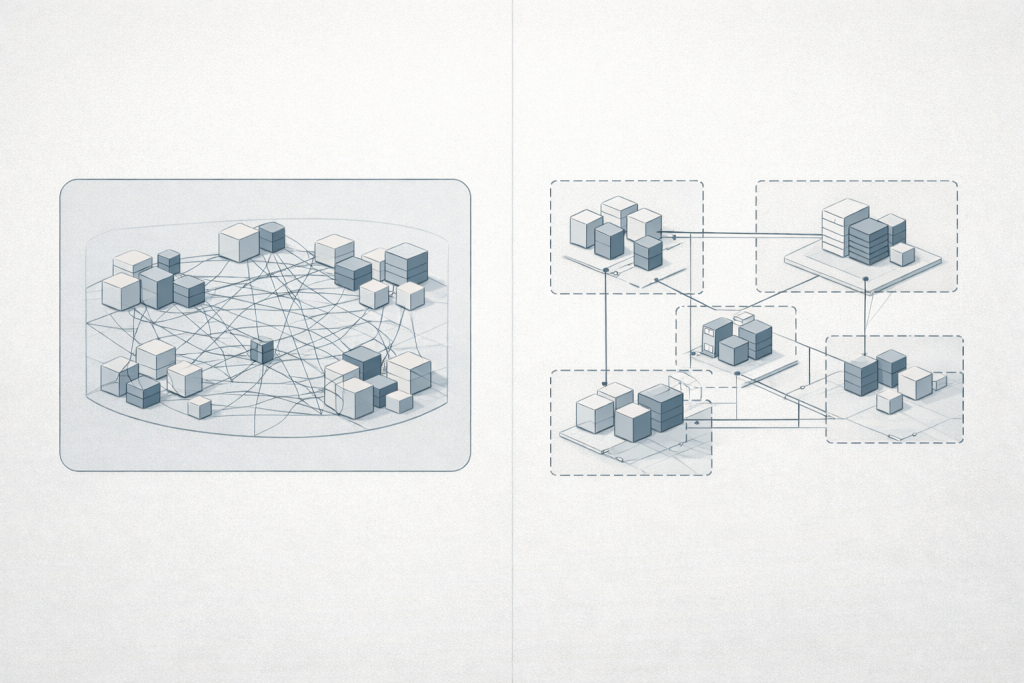
Traditional systems are usually built around a simple idea: danger lives outside, safety exists inside. Once a request has crossed a boundary—after a VPN connection, successful authentication, or entry into an internal network – it is treated as broadly trustworthy. The system assumes that what happens internally is mostly benign, and that excessive checking would only slow things down.
Zero Trust starts from a different premise. It assumes that location alone carries no meaning, and that a previously accepted request does not automatically justify the next one. Trust is not a permanent state. It is a decision made repeatedly, based on context, intent, and observed behavior.
This distinction may sound abstract, but it becomes very concrete the moment something goes wrong.
A Realistic Starting Point: One Compromised Credential
Consider a situation that is technically unremarkable. An attacker gains access to a single credential. It might be an API key embedded in an application, a service account token in a Kubernetes cluster, or a user account with limited privileges. This does not require exceptional skill or rare vulnerabilities. Credentials leak through logs, backups, misconfigurations, and routine operational mistakes.
At this stage, the incident is still small. One entry point, one identity, one foothold. What follows depends entirely on how the system is designed to respond.
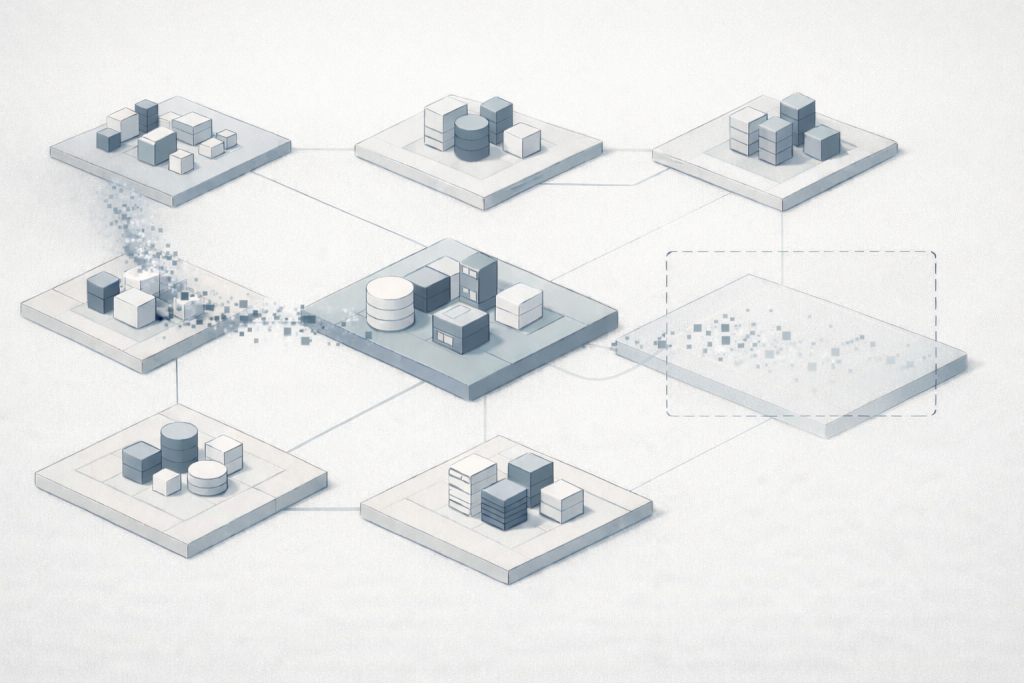
What Happens in a Traditional Architecture
In a conventional setup, that credential is accepted largely at face value. If it is valid, the system allows whatever actions are associated with it. Those permissions are often broader than strictly necessary, granted earlier to simplify operations and rarely revisited. Over time, they become part of the system’s assumed baseline.
Once inside, movement is often straightforward. Internal services can talk to each other because they share a network or a cluster. Databases accept connections because they trust requests originating from inside. Monitoring systems log activity, but the system itself continues to operate as if nothing unusual were happening.
From the attacker’s perspective, this is an environment that rewards patience. There is time to explore, to test which connections work, to observe how components interact. Progress does not require breaking new defenses, only following the paths the system already provides. Everything looks normal because, technically, it is.
The defining characteristic here is continuity of trust. Once granted, it tends to persist.
Zero Trust Begins After the First Mistake
Zero Trust does not promise to prevent that initial credential leak. It does not claim to eliminate human error or configuration drift. Its value emerges only after the first failure.
In a Zero Trust-oriented system, the compromised credential does not automatically unlock broad access. Each request made with that identity is evaluated in context. The system asks not only who is making the request, but what is being requested, where it is going, and whether this behavior matches what is expected.
If no explicit permission exists for that combination, the request fails. Not because an attack has been detected, but because no justification has been established. Progress becomes conditional rather than automatic.
This subtle shift has profound consequences. The attacker’s path narrows quickly. Instead of open-ended exploration, they encounter boundaries defined by purpose, time, and scope.
When Observation Changes Behavior
A key difference between the two models lies in how systems respond to anomalies. In traditional environments, unusual activity is often something that gets recorded and reviewed later. Logs are generated, alerts may be triggered, but the system’s operational behavior remains unchanged.
Zero Trust treats observation as input, not just evidence. When monitoring systems, often centralized log and event collectors such as SIEM platforms, detect behavior that deviates from established patterns, that information feeds back into enforcement.
IF service=backend AND
request_rate > baseline*5 AND
destination not in allowed_service_map
THEN
action = "tighten_policy_for_source"This does not require perfect certainty. The system does not need to label the activity as malicious. It only needs to recognize uncertainty. When uncertainty increases, trust decreases.
Practically, this often manifests at the network level. Traffic from a source that behaves unexpectedly may be restricted to a smaller set of destinations. Connections that were technically possible are no longer permitted unless explicitly required. The system adapts, tightening its posture without human intervention.
In contrast to traditional setups, where anomalies coexist with unchanged access, Zero Trust allows observation to reshape the system’s behavior in real time.
Where Containers Make the Difference Visible
apiVersion: apps/v1
kind: Deployment
metadata:
name: example-app
spec:
replicas: 2
selector:
matchLabels:
app: example-app
template:
metadata:
labels:
app: example-app
spec:
automountServiceAccountToken: false
containers:
- name: app
image: example/app:1.0.0
securityContext:
readOnlyRootFilesystem: true
runAsNonRoot: true
allowPrivilegeEscalation: falseKubernetes environments offer a particularly clear view of this distinction, because trust is encoded directly into configuration. Kubernetes itself is not a Zero Trust platform, but it provides the mechanisms to implement or ignore Zero Trust principles.
Consider what happens once an attacker gains access to a running container.
In many default configurations, a container’s filesystem is writable. Processes run with elevated privileges inside the container. Network access between pods is unrestricted. Service accounts automatically grant access to the Kubernetes API. From a security perspective, this reflects the same assumption as traditional systems: once inside, the environment is largely trusted.
A Zero Trust approach treats this differently.
When a container’s root filesystem is mounted as read-only, the system no longer assumes that the process should be able to modify its own environment. Even if an attacker gains execution inside the container, they cannot install additional tools, alter application binaries, or establish persistence. Everything they do exists only in memory and disappears when the pod restarts.
Running containers as non-root users reinforces this boundary. The process is treated as an application, not as an operating system. Many common exploitation techniques simply fail because the privileges required to use them are absent.
Network policies add another layer. Instead of assuming that any pod can talk to any other, communication is explicitly allowed only where it is required. A compromised pod does not become a stepping stone to the entire cluster. It becomes an isolated endpoint with limited reach.
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: backend-ingress-from-frontend
spec:
podSelector:
matchLabels:
app: backend
policyTypes:
- Ingress
ingress:
- from:
- podSelector:
matchLabels:
app: frontend
ports:
- protocol: TCP
port: 8080
Restricting network paths is often enough to stop lateral movement between services, but it does not address another common escalation route: access to the control plane itself. In Kubernetes environments, this usually means the Kubernetes API. If a compromised pod is able to authenticate against the API server, network isolation alone is no longer sufficient. The attacker can begin enumerating resources, reading configuration, or attempting to create new workloads.
For this reason, Zero Trust thinking extends beyond service-to-service traffic and into workload identity and control-plane access.
apiVersion: v1
kind: Pod
metadata:
name: job-no-k8s-api
spec:
automountServiceAccountToken: false
containers:
- name: job
image: example/job:1.0.0
securityContext:
runAsNonRoot: true
readOnlyRootFilesystem: trueEven access to the Kubernetes API itself is treated cautiously. Pods that do not need to interact with the control plane are not given credentials to do so. This removes one of the most common escalation paths entirely.
None of these measures make attacks impossible. They make them constrained.
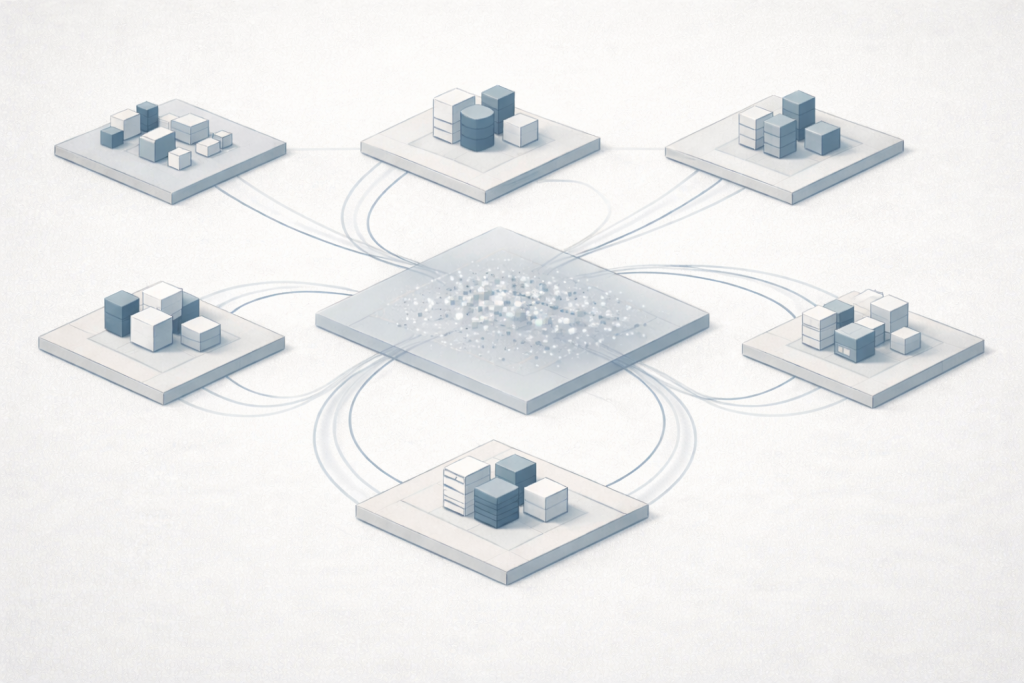
Changing the Shape of Risk
The most important effect of Zero Trust is not prevention, but transformation. In a traditional architecture, a single mistake can open a wide and persistent avenue for abuse. In a Zero Trust-oriented system, the same mistake leads to a narrow, temporary, and fragile opportunity.
From the attacker’s point of view, the environment becomes hostile to slow, methodical progress. Access expires. Routes are blocked. Actions that deviate from expected behavior reduce, rather than expand, available options. What might have been a quiet exploration becomes a race against time and visibility.
This is not a guarantee of safety. It is a shift in dynamics.
An Honest Conclusion
Zero Trust does not eliminate breaches. It does not remove the need for careful engineering or disciplined operations. It does not promise perfect detection or absolute control. What it does offer is a different default response to failure.
Traditional systems tend to preserve trust unless explicitly told not to. Zero Trust systems do the opposite. When certainty erodes, trust contracts.
In practice, this difference often determines whether an incident remains a contained disturbance or grows into a systemic failure. Not because Zero Trust is magical, but because it aligns system behavior with the reality that complex systems will fail – and that resilience begins with how they react when they do.